Latest Trends
Get the latest in Tech,
once a week. Free.

VR/AR
Security
What is a CAPTCHA and Why Does A Website Need Them Anyway?June 4, 2026Security / Web Guides / WordPressEven if you are a very average internet user, you must have had your experiences with CAPTCHAs. Whether its booking movie tickets online, creating email accounts or while accessing various websites; these CAPTCHAs slow us down and tests if we are human. Yeah! They certainly are annoying but since they are meant to serve a specific purpose, let them be. Anyway, there not really is any need to understand what CAPTCHAs are to break them down but for all you enthusiasts; this article will address everything you would like to know about a CAPTCHA.
Okay, so What is a CAPTCHA?
CAPTCHA is a shortened term for ‘Completely Automated Public Turing Test to Tell Computers and Human Apart’. More simply, they are those twisted letters usually with various fonts you mostly encounter during filling online forms. It obviously is a test that is designed for people to prove themselves as a human to the computer. CAPTCHA was first used in 2000 and the most unique feature of this test is, it is very simple for humans. At the same time, it is very difficult for software bots (the automated programs for filling forms).
But, Why use a CAPTCHA?
The main intention behind designing CAPTCHAs is to discourage spammers and hackers in abusing internet resources. The computers and internet bots (automated programs) are very fast, the fact that they are completely built on 1s and 0s makes them weak in identifying things a human can intercept. So for humans, it hardly is a test but for bots, it really is a test!
Okay, we accept it isn’t rocket science and weakly designed CAPTCHAs are easily cracked; Still, there isn’t any universal algorithm in offering these bots human-like intelligence. And still cracking 90% of CAPTCHAs requires a real skill-set hacker.
How These CAPTCHA Work, Actually?
CAPTCHA are usually .gif pictures of scrambled and manipulated letters. These pictures are so designed that they don’t contain the letters on the image in the HTML. So for software bots, it is only an image and the letters on it are non-existent.
The other way around, there are software that can scan these images and interpret the letter present on the image, but it could be possible only if the letters are not so distorted; but that’s not the case with textCAPTCHA.
The mostly used other types of CAPTCHAs are the .mp3 format recordings, in which a distorted voice speaks out letters or words and a human must enter them into the box and submit. This system is so effective that even the CAPTCHA has no idea about the letters being shown.
What all can a CAPTCHA stand against?
CAPTCHAs since their introduction could prevent numerous abusive online activities. These include the blocking of spammers from submitting automated comments to blogs aiming SEO; unnecessary creation of (signing up for) hundreds of email accounts. [...]
Easy Way To Create A Memory Eating Virus – Just For FunJune 2, 2026Notepad Tricks / SecurityToday we are going to teach you one of the easiest ways of creating a virus – with notepad. Yes, simply using your notepad you can perform this awesome trick.
In this article we will show you the process to create a virus that eats up the computer memory i.e Memory Eating Virus. And note that this trick is purely only for educational purpose and OnlineCmag is not responsible for any mishaps in your computer.
Steps To Create A Memory Eating Virus
Step 1 : Creating Two New Text Documents
First of all open a folder in which you would want to create this simple virus . Within it create 2 new text documents in it as shown below .
Step 2 : Customize The First Notepad
Open the first notepad and type ” OnlineCmag.bat ” and save it as ” Ocm.bat ” . ( .Bat extension is must )
Step 3 : Customize The Second Notepad
Now open the second notepad and type ” Ocm.bat ” and save it as ” OnlineCmag.bat ” .
Step 4 : Open any one of these files
Now just Double Click on any one of the saved files . That’s It , Now this virus will start eating up the computer memory. As simple as that. [...]
How to Change Admin Password by Batch ProgrammingMay 31, 2026PC Hacks / SecurityThere are many amazing and simple tricks that help you to change admin password of any computer. Today we are going to show one such simple trick by which you can effortlessly get the job done. Here in this trick we will be using the so called batch programming Technique to change admin password. .
Note : This article is only for educational purpose and OnlineCmag is not responsible for any damage to your computer.
Steps To Change Admin Password :
Step 1 : Open Notepad :
Click on the Start menu and Navigate to All Programs=>Accessories =>Notepad. You can even open it by just typing notepad in your Run .
Step 2 : Copy – Paste :
Copy the below given code carefully and paste it into your notepad . Here ” OnlineCmag ” is the new password which overrides the Old Admin password .
@echo off
NET USER %username% OnlineCmag
DEL pwd.bat
Step 3 : Save It As :
Now save this file with a ” .bat ” extension i.e something like ” pwd.bat ” .
Step 4 : Execute :
Now your file is ready to change any computer’s password . You can copy it into one’s pen-drive and as soon as he/she executes it, the password will be changed to ” OnlineCmag ” .
Share Your Doubts And Views In Comments … [...]
Web Guides
Join Our Tech Community For Free
How To
How To Format A Hard Drive Without Windows Installation CDJune 5, 2026PC HacksIf you have a new hard drive or any used one that you want to clear, Then you need to format your drive. Usually, the easiest way to format a hard drive is to use a Windows installation CD. In-case if you don’t have one, Then don’t feel bad there is nothing to worry you just have to do a little more work that’s it . Formatting a drive is still a simple process, just you have to find the appropriate utilities.
Things Required :
Startup Disk
Steps to Format A Hard Drive :
Step 1 : Configuring the BIOS :
There is really only one way to format a hard drive i.e through some kind of boot device. If not the Windows CD may be a floppy drive or another CD. When the computer starts, it will ask you to press a key to enter the BIOS; must quickly press the indicated key. Once you’re in the BIOS, look through the menus until you get to an option that says something like ” Device Boot Order “. Select ” CD ” or ” CD-ROM “, ” Removable Device ” or something similar, depending on what type of boot device you will be using. Saves the changes and Exit .
Step 2 : Make a boot disk :
You need to download the files from somewhere to make your device Bootable . There are many websites available that has a good selection of files , some are free and some are not.
For a diskette ( floppy ) : Just insert a floppy disk into the drive and run the utility that you have downloaded. This will make your floppy Bootable .
For a CD : You must have a CD burning software. You will have to run the software to copy the files you downloaded and select ” Do this CD bootable ” .
Upon boot device, ensure that one of the utilities you downloaded has a format tool ( you’ll have to read the documentation well ).
Step 3 : Restart the computer :
Start the computer with the BIOS configured correctly and the boot disk instead. The computer will boot from the boot disk or bootable CD. If you’re using the standard DOS boot disk, you can type ” format c: ” (” C ” refers to the hard disk ). If you are using another program, you must use its commands. [...]
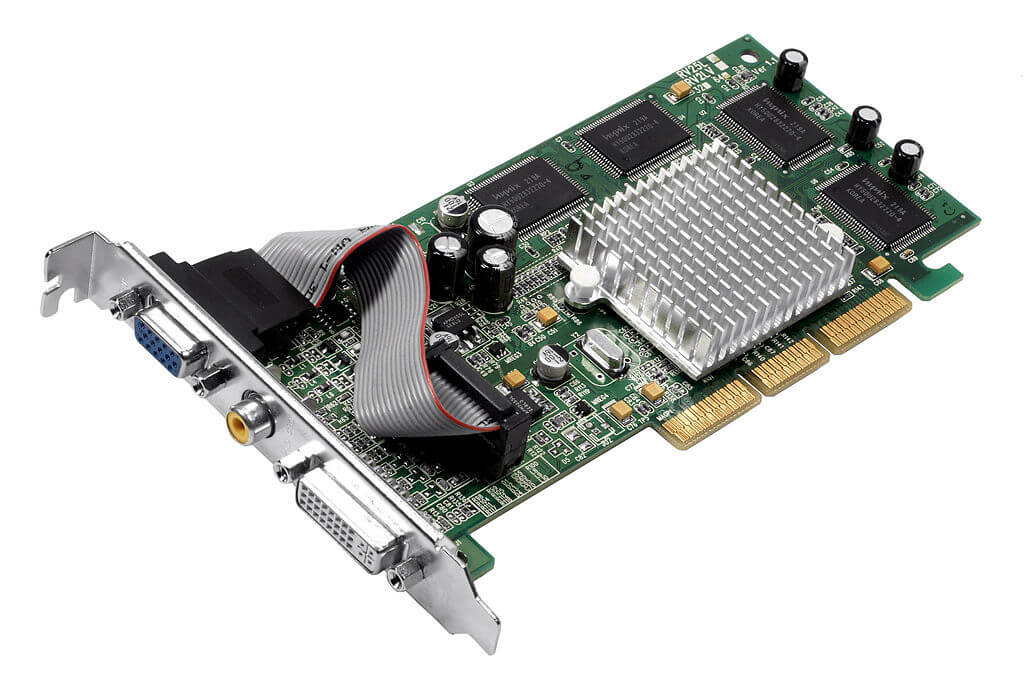
How To Change The Graphics Card Of A LaptopJune 4, 2026PC HacksA graphics card is simply a piece of hardware which connects and sends data to the display screen of your laptop. The quality of the videos displayed on your laptop’s screen is largely depend on this graphic card. You can checkout our article on how the graphics processing unit of a graphic card works here. In general, most of the computers use PCI or PCI Express graphics cards. Installing a graphics card is one of the easiest process in the hardware installations that you can perform on a laptop .
Also See: Common FAQs on Graphic Cards
Things You Need :
A Phillips screwdriver
A flat screwdriver
A wrist strap
Steps You Need To Follow To Change The Graphics Card of a laptop:
Step 1 : Turn off your laptop, unplug the power cord, remove the battery and disconnect all cables and any external device .
Step 2 : Wear an anti-static wrist strap on your wrist, and then place the cable clip on the outer casing of the laptop. This will help you to avoid static electricity discharge.
Step 3 : Open the laptop up to the stop. Use the small flat-head screwdriver to lift the keyboard cover . This cover is basically a small plastic strip located between the keyboard and LCD screen.Remove the cover from the keyboard and keep it aside.
Step 4 : Remove the Phillips head screws securing the keyboard to the portable structure. Pick it up and place it face down on the rest of the notebook. Disconnect the keyboard ribbon connector from the motherboard and then remove the keyboard of the computer and put it aside.
Step 5 : Disconnect the LCD ribbon connector from the video card .
Step 6 : Remove the screw that secures the heat sink to the motherboard. Lift the heat sink base carefully out of your laptop and then keep it aside .
Step 7 : Remove the four screws holding the video card to the motherboard. Lift the old card out of the the base of the laptop and keep it aside. Now install the new video card by placing it in the compartment of the video card and replace the four screws.
Step 8 : Rearrange the laptop by following the steps from 1 to 6 in reverse order.
Step 9 : Insert the disk that came with the new video card into your CD-ROM. Follow the instructions on the screen to install the driver for the new graphics card in your laptop.
Also See: Best Graphic Cards in the Market
Follow all these steps very carefully and simply that’s it! But be sure you handle everything perfectly. [...]
Easy Way To Measure Your CPU TemperatureJune 3, 2026PC Guides / System PerformanceThere are many methods to measure your CPU temperature . Generally the CPU temperature is measured through a ” Temperature sensor ” that is located on the motherboard . Almost ever motherboard comes in with a program which lets you to read this sensor. You can use the applications like ” Hardware Sensors Monitor ” Or ” Motherboard Monitor ” for this task that are available freely .
Motherboard Monitor For Measuring CPU Temperature :
We personally recommend ” Motherboard Monitor ” for measuring your CPU temperature . This program can be directly accessed from the task-bar And it also allows you to set an alarm which will let you know when the CPU reaches its critical temperature level.This application will also monitors the power supply voltages and system fans . This application is highly recommended for the people who overclock their system, As the CPU temperature drastically increases when it is overclocked.
Measuring CPU Temperature By CMOS Setup :
There is also another method to check your CPU temperature i.e though the ” motherboard setup ” . In motherboard setup you will have an option like ” System Health ” Or ” PC Health Status ” Or ” Sensors ” Or something similar based on the manufacturer . The CPU temperature can be easily checked as shown below .
The motherboard setup method is not the right way to check your CPU temperature because it only shows you the temperature at minimum processing power as the system is just started . Thus it won’t reach its maximum temperature. Because of this reason we recommend you a software-based solution like method one . [...]